Contents
show
Resident Monitor and Bare Machine : An Overview
What is resident monitor ?
What is bare machine ?
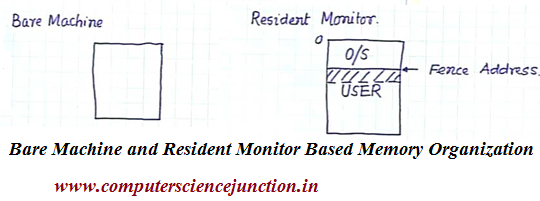
How memory is organized using bare machine and resident monitor ?
This article cover the concept of resident monitor and bare machine in operating system. Article also covers how the memory is organized using bare machine and resident monitor. For the study of Bare machine and Resident monitor I preferred Operating System Concepts: By Galvin
Bare Machine
The simplest variety of organization of main memory is Bare Machine wherever the complete memory is given to the designer, there’s no partition within the memory. Currently it’s up to the designer to make a decision that that a part of the memory can contain the monitor and that part of the memory are going to be used for storing of temporary knowledge, for storage of information, for storage of processed knowledge, everything.
So everything must be set by the system designer. typically this is often the sort of memory organization that is employed for implementation of dedicated systems that’s if I wished to style a laptop that isn’t to be used for general purpose computing.
I will have a laptop for dominant some powerhouse or for dominant some method. in this case the pc that I will be able to use for that operation, i will be able to not wish that laptop to try and do any general purpose computation.
I will have a laptop for dominant some powerhouse or for dominant some method. in this case the pc that I will be able to use for that operation, i will be able to not wish that laptop to try and do any general purpose computation.
Memory organization mistreatment in Bare machine has the subsequent options
- No Protection.
- No Overhead.
- Simplest variety of memory management.
- User have complete control and operating system has none.
- This is used by hardware diagnostics, by the system boot code, real time/dedicated system, maximum flexibility to user and minimum hardware cost.
- No operating system service. It means OS manage nothing instead of its entire address space is given to the program and all the managing left to it.
Resident Monitor
In this section we are going to discuss concerning resident monitor in operating system or resident monitor in memory management. just in case of resident monitor system, the memory is partitioned off, divided into 2 partitions. one among the partition is occupied by the computer program or the software package and therefore the second partition contains the user knowledge or the user program.
User program mustn’t be able to modify something into the monitor space of the memory. Therefore what we have a tendency to primarily would like is protection of the monitor or protection of the software package against any user program.
So however that may be done? Whenever the user program tries to access any of the memory location and memory protection the program can generate the address of the memory location that is to be accessed. Currently if the a part of the memory or the partition among the memory that is occupied by the software package or the monitor is well outlined.
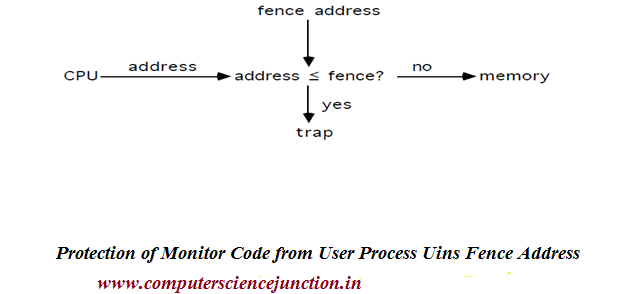
Then I will check on the address that’s being accessed by the user program. If primarily what I actually have to possess is what’s referred to as a fence address.While execution of a user program, the central processor generates the address.
The address of the memory location that’s to be accessed whereas execution of the user program. I even have a fence address that is that the boundary between the user space and therefore the monitor space.
Then I will check on the address that’s being accessed by the user program. If primarily what I actually have to possess is what’s referred to as a fence address.While execution of a user program, the central processor generates the address.
The address of the memory location that’s to be accessed whereas execution of the user program. I even have a fence address that is that the boundary between the user space and therefore the monitor space.
Therefore I actually have to check this fence address with the address that’s generated by the central processor. therefore I actually have to check these 2 addresses. In such a system, the hardware should defend the monitor code (OS code) from the user; usually|this can be} often finished a fence address as follows:
Figure 2: Protection of Monitor Space using fence address.
Must check every memory reference against fence ( mounted or variable ) in hardware or register. If user generated address < fence address, then illegal access.
Keywords: definition of resident monitor, what is bare machine, definition of fence address,logical address,memory, operating system code protection , user process, resident monitor in os, resident monitor in operating system, basic bare machine in memory management